Our Journey to Understand Cyber Adversaries
July 2018, our team delivered a presentation to the Waterloo-Regional Police on cyber capabilities we could develop on their behalf, changing the course of our company forever. Our small team realized an industrywide need to understand advanced operator tactics and the need to know which of these tactics were currently in vogue. We decided to employ automation to collect adversary behaviors from the wild so that we could analyze the tactics being used – our first cyber intelligence engine was born, Harvester.
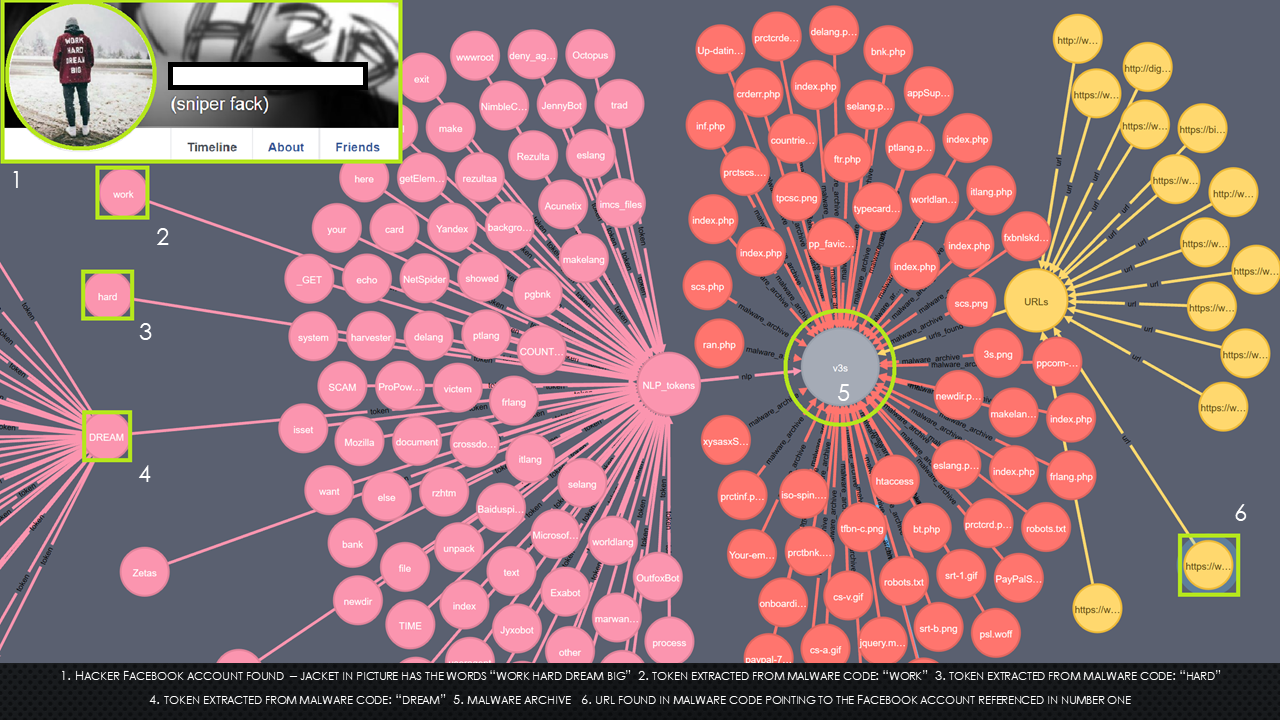
Harvester was an interesting and effective piece of technology. At its ingress, Harvester utilized a classifier to scan the certificate transparency logs for anomalous domain registrations which indicated fraud. During processing, the automation would go out and download a copy of the phishing kit being used (provided it was accessible) and then dismantle the code syntax into linguistic tokens. At the core of Harvester’s technology was the theory of linguistic fingerprinting, as criminal hackers like to use a lexicon that can be quite unique, almost like a fingerprint. At Harvester’s egress, the technology would produce linguistic fingerprints of criminal adversaries that had been processed and correlated within the automation and graph database. Our analysts would then manually query large social platforms with these fingerprints and attempt to link them to the adversaries they represented. Although very time consuming, this resulted in the fairly consistent attribution of individuals behind the financially motivated criminal campaigns (carding campaigns), that Harvester initially ingested. This attribution allowed us to manually infiltrate criminal development circles and examine other tradecraft the criminals were utilizing or intending to use. Again, effective but time consuming due to all the manual analysis needed to distill the operator tactics.
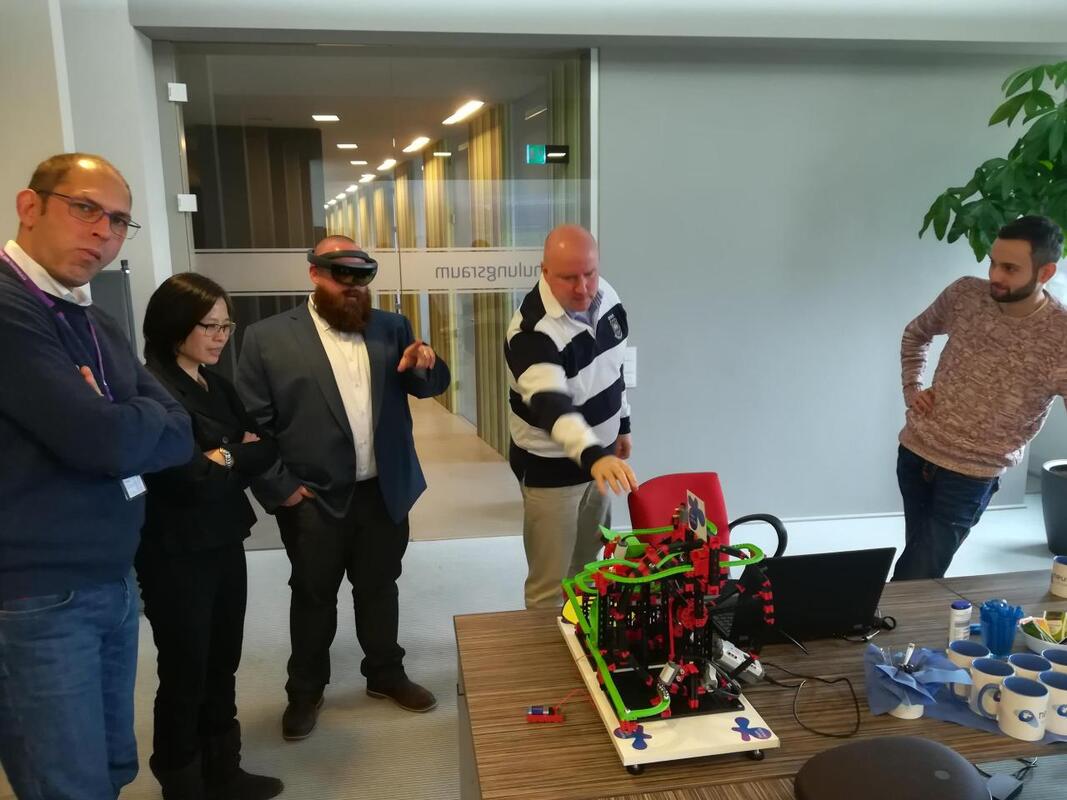
Cyber Mongol’s use of automation and big data technologies within the context of cybersecurity allowed us to secure a spot with the Canadian / German Transatlantic Delegation for Big Data and Cybersecurity, November 2018. As a delegate, we met with business leaders and subject matter experts across the Ruhr region, crosspollinating ideas and exchanging expertise. This trip inspired our company’s vision to grow in two ways; first, we would need to increase “smart” automation to get to the operator tactics with much less analyst intervention. The second, we were enthused by the Germans use of XR (augmented reality) technologies to expound advanced skillset trainings (maintaining critical infrastructure with robotics and virtual reality). We knew we needed a new way to deliver advanced cyber operator training that was not blogs or video.
After the insights realized in Germany, our team got hard to work turning abstract requirements into reality. Through our research, we noticed that adversaries utilized thorough and sometimes sophisticated surveillance structures to consume innovation from within the security community. We would see security researcher content being shared and talked about on criminally controlled communication assets, social media channels and adversary blogs and manifestos. It became increasingly clear that advanced operators looked to the elite in the security community for ways in which to migrate their tradecraft. The security community is an abstract concept that can be made up of things like source code repositories, social media channels, elite influencers (both criminal and researcher), community chatter, trending news and vendor blogs. We realized that if we could autonomously collect, correlate, triage and classify these vast signals emanating from the community, an enormous amount of intelligence could be gleaned without the human expenditure. This was the birth of the PANDEMIC cyber threat intelligence engine.
With half the requirements in Germany now realized, the team set out to build a new way to convey these advanced signals and tactics intelligence. An early prototype codenamed Guru was born, utilizing a cutting-edge conversational interface to articulate operator tradecraft, searchable signal feeds which allowed direct access to underlying signal assets and enumeration of the offensive cybersecurity ecosystem with a dynamic graph visualization. This advanced prototype granted us the opportunity to be selected as a tier one exhibitor at RSA 2020, housed within the Government of Ontario’s tech pavilion. Guru’s conversational interface went on to become a product within itself (ASATA), specializing in articulating advanced, offensive cyber-tradecraft through the use of conversation. At this point our team realized we had been developing our capabilities around one fundamental concept, core to all our technologies - human-machine-teaming.